Bruno Stelmaszyk - książki
Tytuły autora: dostępne w księgarni Ebookpoint
-
API Security for White Hat Hackers. Uncover offensive defense strategies and get up to speed with secure API implementation
-
Computer Networks in Packet Tracer for beginners
-
Packet Tracer for young beginning admins
-
Cloud Auditing Best Practices. Perform Security and IT Audits across AWS, Azure, and GCP by building effective cloud auditing plans
-
Po pierwsze: bezpieczeństwo. Przewodnik dla twórców oprogramowania
-
Etyczny haking. Praktyczne wprowadzenie do hakingu
-
Windows and Linux Penetration Testing from Scratch. Harness the power of pen testing with Kali Linux for unbeatable hard-hitting results - Second Edition
-
Check Point Firewall Administration R81.10+. A practical guide to Check Point firewall deployment and administration
-
Mastering Windows Security and Hardening. Secure and protect your Windows environment from cyber threats using zero-trust security principles - Second Edition
-
Purple Team Strategies. Enhancing global security posture through uniting red and blue teams with adversary emulation
-
The Foundations of Threat Hunting. Organize and design effective cyber threat hunts to meet business needs
-
Ochrona cyberprzestrzeni Unii Europejskiej
-
Hakowanie internetu rzeczy w praktyce. Przewodnik po skutecznych metodach atakowania IoT
-
Cybersecurity Leadership Demystified. A comprehensive guide to becoming a world-class modern cybersecurity leader and global CISO
-
Bezpieczeństwo sieci w Pythonie. Rozwiązywanie problemów za pomocą skryptów i bibliotek. Wydanie II
-
Cybersecurity Career Master Plan. Proven techniques and effective tips to help you advance in your cybersecurity career
-
Creative DIY Microcontroller Projects with TinyGo and WebAssembly. A practical guide to building embedded applications for low-powered devices, IoT, and home automation
-
API Testing and Development with Postman. A practical guide to creating, testing, and managing APIs for automated software testing
-
AWS Penetration Testing. Beginner's guide to hacking AWS with tools such as Kali Linux, Metasploit, and Nmap
-
Amazon Web Services w akcji. Wydanie II
-
Hands-On RESTful Web Services with Go. Develop elegant RESTful APIs with Golang for microservices and the cloud - Second Edition
-
Learning CoreDNS. Configuring DNS for Cloud Native Environments
-
Python Network Programming. Conquer all your networking challenges with the powerful Python language
-
Bądź bezpieczny w cyfrowym świecie. Poradnik bezpieczeństwa IT dla każdego
-
Mastering Python for Networking and Security. Leverage Python scripts and libraries to overcome networking and security issues
-
Hands-On Penetration Testing on Windows. Unleash Kali Linux, PowerShell, and Windows debugging tools for security testing and analysis
-
Hands-On Cryptography with Python. Leverage the power of Python to encrypt and decrypt data
-
Learning Python Web Penetration Testing. Automate web penetration testing activities using Python
-
CCNA Security 210-260 Certification Guide. Build your knowledge of network security and pass your CCNA Security exam (210-260)
-
Mastering Wireshark 2. Develop skills for network analysis and address a wide range of information security threats
-
Metasploit Penetration Testing Cookbook. Evade antiviruses, bypass firewalls, and exploit complex environments with the most widely used penetration testing framework - Third Edition
-
Security with Go. Explore the power of Golang to secure host, web, and cloud services
-
Bezpieczeństwo aplikacji mobilnych. Podręcznik hakera
-
JUNOS Automation Cookbook. Automate network devices on Juniper's operating system
-
Network Security Through Data Analysis. From Data to Action. 2nd Edition
-
Penetration Testing Bootcamp. Quickly get up and running with pentesting techniques
-
Kali Linux Network Scanning Cookbook. A Step-by-Step Guide leveraging Custom Scripts and Integrated Tools in Kali Linux - Second Edition
-
Applied Network Security. Proven tactics to detect and defend against all kinds of network attack
-
Mroczne odmęty phishingu. Nie daj się złowić!
-
Penetration Testing with Raspberry Pi. A portable hacking station for effective pentesting - Second Edition
-
Kali Linux 2 - Assuring Security by Penetration Testing. Achieve the gold standard in penetration testing with Kali using this masterpiece, now in its third edition! - Third Edition
-
Building Virtual Pentesting Labs for Advanced Penetration Testing. Click here to enter text. - Second Edition
-
Monitorowanie aktywności użytkowników systemów komputerowych
-
Podpis cyfrowy i identyfikacja użytkowników w sieci Internet
-
Mastering Python Forensics. Master the art of digital forensics and analysis with Python
-
Accumulo. Application Development, Table Design, and Best Practices
-
Untangle Network Security. Secure your network against threats and vulnerabilities using the unparalleled Untangle NGFW
-
Profesjonalne testy penetracyjne. Zbuduj własne środowisko do testów
-
VMware View Security Essentials. The vital elements of securing your View environment are the subject of this user-friendly guide. From a theoretical overview to practical instructions, it's the ideal tutorial for beginners and an essential reference source for the more experienced
-
BackTrack - Testing Wireless Network Security. Secure your wireless networks against attacks, hacks, and intruders with this step-by-step guide
-
Bezpieczeństwo systemu e-commerce, czyli jak bez ryzyka prowadzić biznes w internecie
-
Podstawy ochrony komputerów
-
Profesjonalne tworzenie kopii zapasowych i odzyskiwanie danych
-
13 najpopularniejszych sieciowych ataków na Twój komputer. Wykrywanie, usuwanie skutków i zapobieganie
-
Active Directory Disaster Recovery. Expert guidance on planning and implementing Active Directory disaster recovery plans with this book and
-
ScreenOS Cookbook
-
SSH, The Secure Shell: The Definitive Guide. The Definitive Guide. 2nd Edition
-
Snort Cookbook
-
RADIUS. Securing Public Access to Private Resources
-
Web Security, Privacy & Commerce. 2nd Edition
-
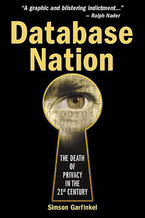
Database Nation. The Death of Privacy in the 21st Century
-
Building Internet Firewalls. 2nd Edition
-
Microsoft Windows Server 2022. Kurs video. Zaawansowane techniki administrowania siecią
-
Elastic Stack. Kurs video. Monitoring aplikacji i systemów IT
-
Zabbix. Kurs video. Monitoring systemów IT
-
Sieci VPN. Kurs video. OpenVPN i Wireguard w praktyce
-
Modern Network Observability. A hands-on approach using open-source tools such as Telegraf, Prometheus, Grafana, and other tools
-
Bezpieczeństwo sieci w Linuksie. Wykrywanie ataków i obrona przed nimi za pomocą iptables, psad i fwsnort